As the technology is progressing that much new devices are coming into the market. Most of every new device or any gadget is capable of connecting with Wi-Fi Networks. People are even getting addicted to it, so there's nothing new that in coming years it will progress more. Looking at this, to give an ease to people and also to achieve advancement in business through technology wise, Public Wi-Fi hot spots, are on high demand.
No doubt, Public Wi-Fi does offers convenience, and it’s accessible and operated in several home, office premises, university campus, and even public hot spots are available throughout the world. Everyone has used it, whether it is from Airport, coffee shop, any library, park or hotel, mostly all are having these open Wi-Fi networks.
Everyone might not be aware of but it comes with certain threats, public Wi-Fi are mostly un-encrypted, which literally means that anyone can hack into every data sent over network by using easily available cheap software.
Below are some of the most possible associated risks by the use of public Wi-Fi:
Sniffers: By the use of software sniffers, hackers can passively intercept data sent between the web browser and web server. Due to this, they can capture any email, web search or file transferred on an unsecured network.
Evil Twin: An Evil Twin is a poor Wi-Fi connection which looks legit, but it is actually set up by a hacker to fool users connecting with Wi-Fi connection. Once a user get connected, hacker can look up to all the internet traffic and can even ask for confidential information such as credit card details, showing themselves as legit pay to access deal.
Man-in-the-Middle Attacks: It is one of the most possible and occurring attack. In this any device between user and an intended network server can become a victim, due to which intercept and tampering of data exchanged between the user and server is possible.
Side-jacking: It is a type of attacking method, where an attacker make use of packet sniffer, type of program which can intercept or log traffic passing over a network, in order to steal session cookie which contains vital information like usernames and passwords from several websites like Facebook, Gmail, etc.
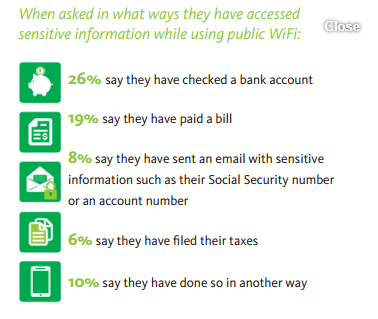
Mostly people are not taking any step to protect themselves while making use of any Public Wi-Fi. Maybe because, people are not fully aware about the threats which are possible on using it. By looking at the below survey, you can easily know how dangerous it can become if someone becomes a victim due to use of Public Wi-Fi.
Though risk of using public Wi-Fi is inherent, but there are certain security methods which can be used to stop threats. No doubt,Anti-virus software, Firewalls & HTTPS does play a vital role in providing online security but they are not enough when it comes to public Wi-FI. Though no need to worry, there’s a solution and it’s VPN (Virtual Private Network), it is a technology which address every problem associated with public Wi-Fi.
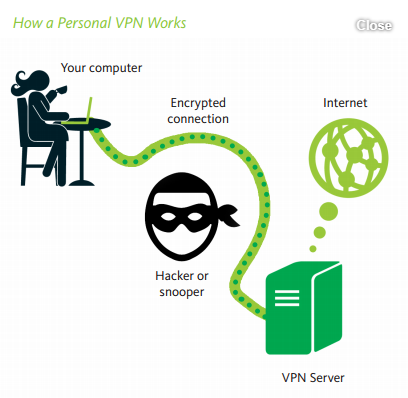
By looking at the above figure you can know that how it works. It encrypts all the data which is passed through user’s computer or mobile devices to server, and both the side uses the same encryption algorithm and key. Due to this technology, hackers get blocked and will not be able to success in any of its attempt to intercept or making change of data, no matter which method they apply.
Moreover, The principal disadvantages to using public Wi-Fi are, passive and active.
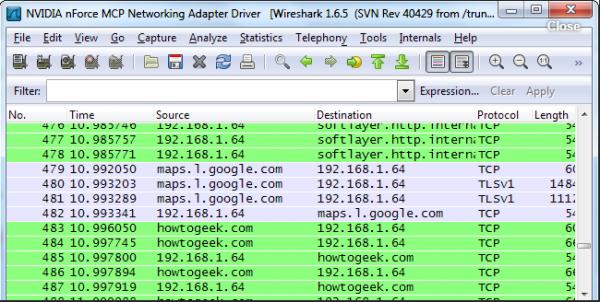
Passively, your traffic can be sniffed or intercepted by other parties on or near the network - without even being connected if they place their card in "monitor" mode and home in on your network card's nominally unique address. Using tools such as Wireshark, they can then intercept email, listen to VOIP conversations, read IM's and otherwise enjoy your traffic, including stealing cookies to authenticate themselves as you to web sites.
Actively, you become vulnerable to "Man in the Middle" (MiTM) attacks, which allow an attacker to intersplice themself between you and a web page you are visiting - one famous tool replaces all images loading on pages with those of sheep - or even usurp the identity of the router altogether. This allows them to hijack an incautious user's banking sessions, access all kinds of porn under your address, and generally prank you to hell and back, not to mention injecting hostile code on otherwise trusted pages which can then infect your computer with a more lasting lament.
That's why there is a saying that “Don’t do your online banking or anything sensitive on a public Wi-Fi network.” The advice is out there, but why can using a public Wi-Fi network actually be dangerous? And wouldn’t online banking be secure, as it’s encrypted?
There are a few big problems with using a public Wi-Fi network. The open nature of the network allows for snooping, the network could be full of compromised machines, or — most worryingly — the hotspot itself could be malicious.
Snooping
Encryption normally helps protect your network traffic from prying eyes. For example, even if your neighbor at home is within range of your Wi-Fi network, they can’t see the web pages you’re viewing. This wireless traffic is encrypted between your laptop, tablet, or smartphone and your wireless router. It’s encrypted with your Wi-Fi passphrase.
When you connect to an open Wi-Fi network like one at a coffee shop or airport, the network is generally unencrypted — you can tell because you don’t have to enter a passphrase when connecting. Your unencrypted network traffic is then clearly visible to everyone in range. People can see what unencrypted web pages you’re visiting, what you’re typing into unencrypted web forms, and even see which encrypted websites you’re connected to — so if you’re connected to your bank’s website, they’d know it, although they wouldn’t know what you were doing.
This was illustrated most sensationally with Firesheep, an easy-to-use tool that allows people sitting in coffee shops or on other open Wi-Fi networks to snoop on other people’s browsing sessions and hijack them. More advanced tools like Wireshark could also be used to capture and analyze traffic.
Protecting Yourself: If you’re accessing something sensitive on public Wi-Fi, try to do it on an encrypted website. The HTTPS Everywhere browser extension can help with this by redirecting you to encrypted pages when available. If you frequently browse on public Wi-Fi, you may want to pay for a VPN and browse through it when on public Wi-Fi. Anyone in the local area will only be able to see that you’re connected to the VPN, not what you’re doing on it.
Also go through this magnificent article by De Correspondent (Crowd Sourced Journalism Website) to understand the repercussions of using Public Wi-Fi -
In his backpack, Wouter Slotboom, 34, carries around a small black device, slightly larger than a pack of cigarettes, with an antenna on it. I meet Wouter by chance at a random café in the center of Amsterdam. It is a sunny day and almost all the tables are occupied. Some people talk, others are working on their laptops or playing with their smartphones.
Wouter removes his laptop from his backpack, puts the black device on the table, and hides it under a menu. A waitress passes by and we ask for two coffees and the password for the WiFi network. Meanwhile, Wouter switches on his laptop and device, launches some programs, and soon the screen starts to fill with green text lines. It gradually becomes clear that Wouter’s device is connecting to the laptops, smartphones, and tablets of local cafe visitors.
On his screen, phrases like “iPhone Joris” and “Simone’s MacBook” start to appear. The device’s antenna is intercepting the signals that are being sent from the laptops, smartphones, and tablets around us.
We learn that Joris had previously visited McDonald’s, probably spent his vacation in Spain, and had been kart-racing.
More text starts to appear on the screen. We are able to see which WiFi networks the devices were previously connected to. Sometimes the names of the networks are composed of mostly numbers and random letters, making it hard to trace them to a definite location, but more often than not, these WiFi networks give away the place they belong to.
We learn that Joris had previously visited McDonald’s, probably spent his vacation in Spain (lots of Spanish-language network names), and had been kart-racing (he had connected to a network belonging to a well-known local kart-racing center). Martin, another café visitor, had been logged on to the network of Heathrow airport and the American airline Southwest. In Amsterdam, he’s probably staying at the White Tulip Hostel. He had also paid a visit to coffee shop called The Bulldog.
Session 1: Let everyone connect to our fake network
The waitress serves us our coffee and hands us the WiFi password. After Slotboom is connected, he is able to provide all the visitors with an internet connection and to redirect all internet traffic through his little device.
Most smartphones, laptops, and tablets automatically search and connect to WiFi networks. They usually prefer a network with a previously established connection. If you have ever logged on to the T-Mobile network on the train, for example, your device will search for a T-Mobile network in the area.
My phone automatically connects itself to one of these networks, which all belong to the black device.
Slotboom’s device is capable of registering these searches and appearing as that trusted WiFi network. To demonstrate, I suddenly see the name of my home network appear on my iPhone’s list of available networks, as well as my workplace, and a list of cafes, hotel lobbies, trains, and other public places I’ve visited. My phone automatically connects itself to one of these networks, which all belong to the black device.
Slotboom can also broadcast a fictitious network name, making users believe they are actually connecting to the network of the place they’re visiting. For example, if a place has a WiFi network consisting of random letters and numbers (Fritzbox xyz123), Slotboom is able to provide the network name (Starbucks). People, he says, are much more willing to connect to these.
We see more and more visitors log on to our fictitious network. The siren song of the little black device appears to be irresistible. Already 20 smartphones and laptops are ours. If he wanted to, Slotboom is now able to completely ruin the lives of the people connected: He can retrieve their passwords, steal their identity, and plunder their bank accounts. Later today, he will show me how. I have given him permission to hack me in order to demonstrate what he is capable of, though it could be done to anyone with a smartphone in search of a network, or a laptop connecting to a WiFi network.
Everything, with very few exceptions, can be cracked.
The idea that public WiFi networks are not secure is not exactly news. It is, however, news that can’t be repeated often enough. There are currently more than 1.43 billion smartphone users worldwide Find the latest numbers hereand more than 150 million smartphone owners in the U.S. In the U.S., more than 92 million American adults Tablet numbersown a tablet and more than 155 million The census has numbersown a laptop. Each year the worldwide demand for more laptops and tablets increases. In 2013, an estimated 206 million tablets and 180 million laptops were sold worldwide. Probably everyone with a portable device has once been connected to a public WiFi network: while having a coffee, on the train, or at a hotel.
Everything, with very few exceptions, can be cracked.
The good news is that some networks are better protected than others; some email and social media services use encryption methods that are more secure than their competitors. But spend a day walking in the city with Wouter Slotboom, and you’ll find that almost everything and everyone connected to a WiFi network can be hacked. A study Read the study herefrom threat intelligence consultancy, Risk Based Security, estimates that more than 822 million records were exposed worldwide in 2013, including credit card numbers, birth dates, medical information, phone numbers, social security numbers, addresses, user names, emails, names, and passwords. Sixty-five percent of those records came from the U.S. According to IT security firm Kaspersky Lab, in 2013 an estimated 37.3 million users worldwide and 4.5 million Americans were the victim of phishing—or pharming—attempts, meaning payment details were stolen from hacked computers, smartphones, or website users.
Report after report shows that digital identity fraud is an increasingly common problem. Hackers and cybercriminals currently have many different tricks at their disposal. But the prevalence of open, unprotected WiFi networks does make it extremely easy for them. The National Cyber Security Center, a division of the Ministry of Security and Justice, did not issue the following advice in vain: “It is not advisable to use open WiFi networks in public places. If these networks are used, work or financial related activities should better be avoided.”
Slotboom calls himself an “ethical hacker,” or one of the good guys; a technology buff who wants to reveal the potential dangers of internet and technology. He advises individuals and companies on how to better protect themselves and their information. He does this, as he did today, usually by demonstrating how easy it is to inflict damage. Because really, it’s child’s play: The device is cheap, the software for intercepting traffic is very easy to use, and readily available for downloaded. “All you need is 70 Euros, an average IQ, and a little patience,” he says. I will refrain from elaborating on some of the more technical aspects, such as equipment, software, and apps needed to go about hacking people.

Session 2: Scanning for Names, Passwords and Sexual Orientation
Armed with Slotboom’s backpack, we move to a coffeehouse that is known for the beautiful flowers drawn in the foam of the lattes, and as a popular spot for freelancers working on laptops. This place is now packed with people concentrating on their screens.
Slotboom switches on his equipment. He takes us through the same steps, and within a couple of minutes, 20 or so devices are connected to ours. Again we see their Mac-addresses and login history, and in some cases their owners names. At my request, we now go a step further.
Slotboom launches another program (also readily available for download), which allows him to extract even more information from the connected smartphones and laptops. We are able to see the specifications of the mobile phone models (Samsung Galaxy S4), the language settings for the different devices, and the version of the operating system used iOS 7.0.5).
The latter can be extremely valuable information for a malicious hacker. If a device has an outdated operating system, for example, there are always known “bugs,” or holes in the security system that can be easily exploited. With this kind of information, you have what you need to break into the operating system and take over the device. A sampling of the coffeehouse customers reveals that none of the connected devices have the latest version of the operating system installed. For all these legacy systems, a known bug is listed online.
We see that one visitor has the gay dating app Grindr installed on his smartphone.
We can now see some of the actual internet traffic of those around us. We see that someone with a MacBook is browsing the site Het laatste nieuws het eerst op NU.nl. We can see that many devices are sending documents using WeTransfer, some are connecting to Dropbox, and some show activity on Tumblr. We see that someone has just logged on to FourSquare. The name of this person is also shown, and, after googling his name, we recognize him as the person sitting just a few feet away from us.
Information comes flooding in, even from visitors who are not actively working or surfing. Many email programs and apps constantly make contact with their servers—a necessary step for a device to retrieve new emails. For some devices and programs, we are able to see what information is being sent, and to which server.
And now it’s getting really personal. We see that one visitor has the gay dating app Grindr installed on his smartphone. We also see the name and type of the smartphone he’s using (iPhone 5s). We stop here, but it would be a breeze to find out to who the phone belongs to. We also see that someone’s phone is attempting to connect to a server in Russia, sending the password along with it, which we are able to intercept.
Session 3: Checking out Studies, Hobbies and Relationship Problems
Many apps, programs, websites, and types of software make use of encryption technologies. These are there to ensure that the information sent and received from a device is not accessible to unauthorized eyes. But once the user is connected to Slotboom’s WiFi network, these security measures can be circumvented relatively easily, with the help of decryption software.
To our shared surprise, we see an app sending personal information to a company that sells online advertising. Among other things, we see the location data, technical information of the phone, and information of the WiFi network. We can also see the name (first and last) of a woman using the social bookmarking website,Delicious. Delicious allows users to share websites—bookmarks—they are interested in. In principle, the pages that users of Delicious share are available publicly, yet we can’t help feeling like voyeurs when we realize just how much we are able to learn about this woman on the basis of this information.
First we google her name, which immediately allows us to determine what she looks like and where in the coffeehouse she is sitting. We learn that she was born in a different European country and only recently moved to the Netherlands. Through Delicious we discover that she’s been visiting the website of a Dutch language course and she has bookmarked a website with information on the Dutch integration course.
In less than 20 minutes, here’s what we’ve learned about the woman sitting 10 feet from us: where she was born, where she studied and that she has an interest in yoga.
In less than 20 minutes, here’s what we’ve learned about the woman sitting 10 feet from us: where she was born, where she studied, that she has an interest in yoga, that she’s bookmarked an online offer for an anti-snore mantras, recently visited Thailand and Laos, and shows a remarkable interest in sites that offer tips on how to save a relationship.
Slotboom shows me some more hacker tricks. Using an app on his phone, he is able to change specific words on any website. For example, whenever the word “Opstelten” (the name of a Dutch politician) is mentioned, people see the word “Dutroux” (the name of a convicted serial killer) rendered on the page instead. We tested it and it works. We try another trick: Anyone loading a website that includes pictures gets to see a picture selected by Slotboom. This all sounds funny if you’re looking for some mischief, but it also makes it possible to load images of child pornography on someone’s smartphone, the possession of which is a criminal offense.

Password Intercepted
We visit yet another cafe. My last request to Slotboom is to show me what he would do if he wanted to really harm me. He asks me to go to Sign In (the Microsoft email site) and enter a random username and password. A few seconds later, the information I just typed appears on his screen. “Now I have the login details of your email account,” Slotboom says. “The first thing I would do is change the password of your account and to indicate to other services you use that I have forgotten my password. Most people use the same email account for all services. And those new passwords will then be sent to your mailbox, which means I will have them at my disposal as well.” We do the same for Facebook: Slotboom is able to intercept the login name and password I entered with relative ease.
Within 20 minutes he’s obtained the login details, including passwords for my Sign In, SNS Bank, Facebook, and DigiD accounts.
Another trick that Slotboom uses is to divert my internet traffic. For example, whenever I try to access the webpage of my bank, he has instructed his program to re-direct me to a page he owns: a cloned site that appears to be identical to the trusted site, but is in fact completely controlled by Slotboom. Hackers call this DNS spoofing. The information I entered on the site is stored on the server owned by Slotboom. Within 20 minutes he’s obtained the login details, including passwords for my Sign In, SNS Bank, Facebook, and DigiD accounts.
I will never again be connecting to an insecure public WiFi network without taking security measures.
